What does Tilde.run actually do?
The promise of autonomous AI agents is that they can handle repetitive, time-consuming tasks — code review, data processing, document writing — without human fatigue. But the moment you let an AI agent touch your actual production infrastructure (a GitHub repo with write access, an S3 bucket with production data, a database with live records), the risk becomes unacceptable. A single misconfigured agent instruction can force-push to main, delete the wrong files, or overwrite production data. Most teams want the efficiency of autonomous agents but cannot accept the risk of irreversible mistakes. The result is that many teams either do not use autonomous agents in production at all, or they wrap them in so many safety checks that the efficiency gain disappears.
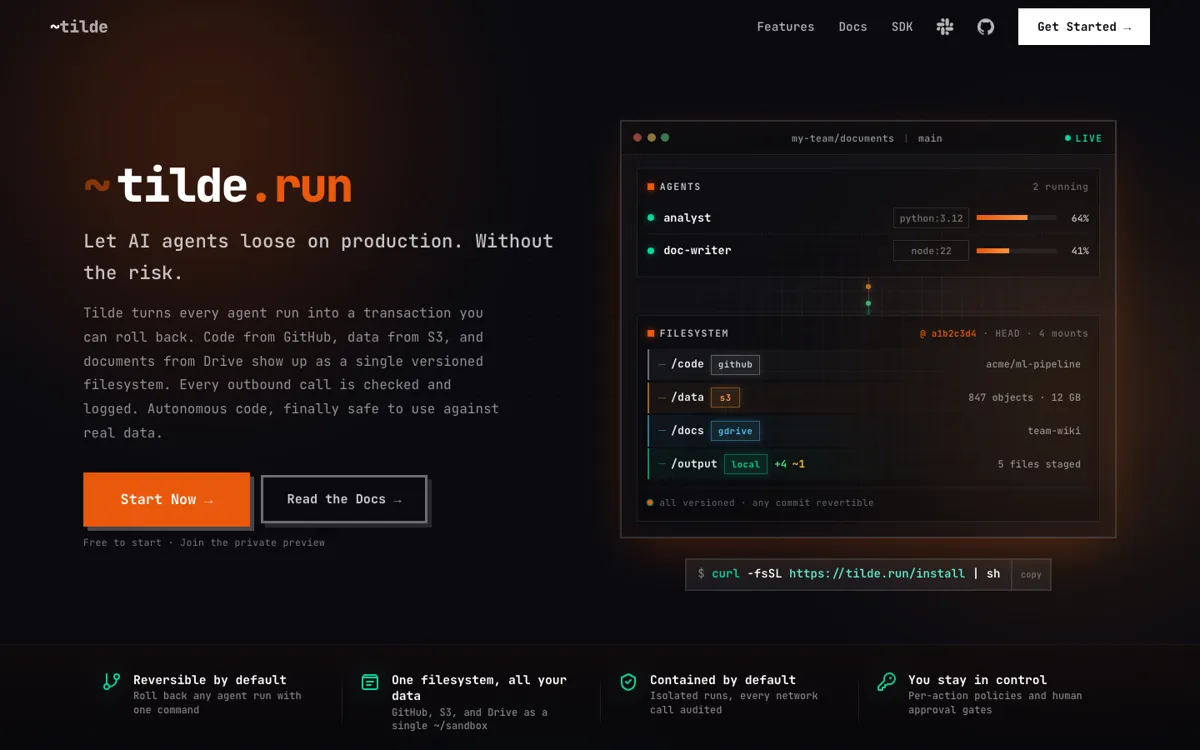
Tilde.run wraps every agent action in a rollback guarantee — before the agent makes any change, Tilde takes a snapshot. If the agent makes a wrong decision or takes an unintended action, you trigger a rollback and Tilde restores the filesystem to the pre-action state. Each agent also runs in an isolated sandbox environment, so a rogue instruction cannot affect your actual production systems unless you explicitly approve the agent's proposed action. You configure the agent, set its permissions and constraints, and Tilde handles the isolation, execution, and rollback layer. The agent works against your real GitHub repos, S3 buckets, and Google Drive — not simulated environments — so the output is real.